Show summary Hide summary
At Black Hat Las Vegas 2025, veteran security expert Mikko Hyppönen sketched a blunt reality: most defensive work goes unnoticed until it fails. That invisibility — and a new battlefield defined by unmanned aircraft — helps explain why one of the field’s oldest voices has shifted from tracking viruses to defending against drones.
Hyppönen, whose career spans the transition from floppy-disk viruses to modern cyber-espionage, described the move as both pragmatic and personal. Living near Finland’s eastern border and watching the role of drones in Russia’s war in Ukraine convinced him the next major threat won’t arrive via email attachments alone.
From tinkering with games to tracing global outbreaks
He began in the 1980s as a hobbyist, reverse-engineering copy protection on home computers and writing small games. That curiosity led to a job analyzing malicious software at a Finnish firm that later became well-known for antivirus products, and then to a decades-long role as a public-facing commentator on cyberthreats.
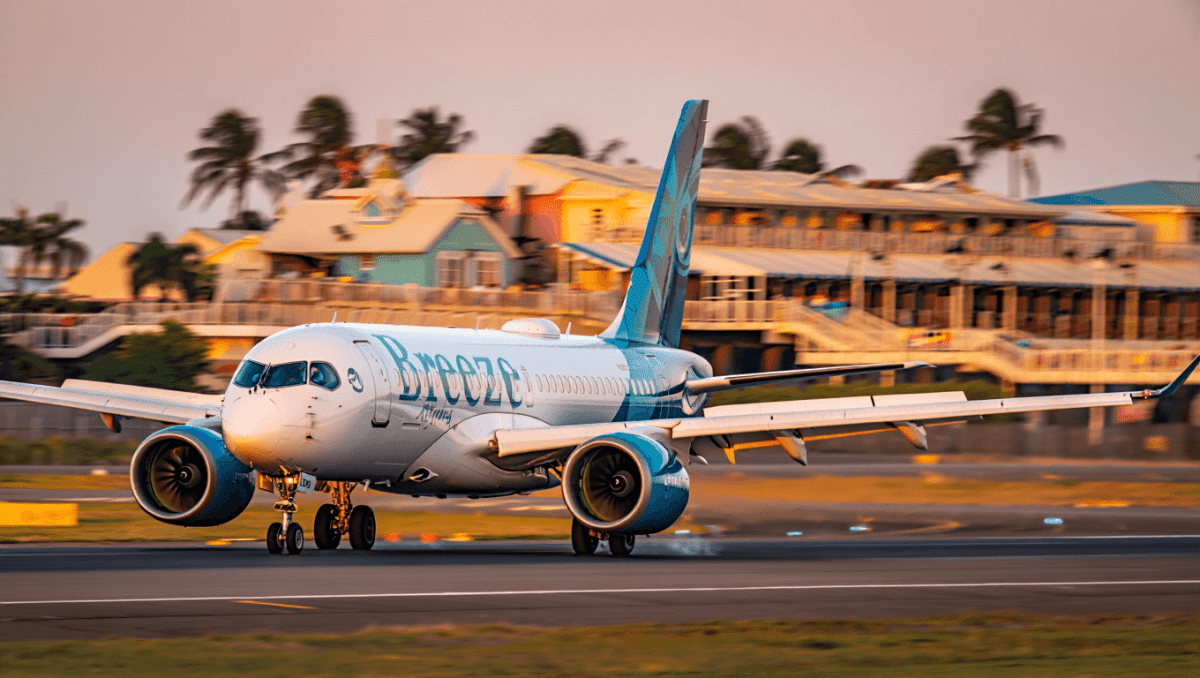
Breeze Airways launches 5 new international routes in Caribbean
Roaring Kitty’s X account posts after 16 months, GameStop jumps 13%
Over the years Hyppönen has analyzed thousands of samples, seen whole families of malware evolve, and helped identify some of the era-defining outbreaks — the early floppy-disk–borne infections, the mass-mailing worms that spread through inboxes, and later, destructive campaigns that disrupted entire networks.
He notes a major shift in motive and method. Where once many authors experimented for fun or notoriety, today’s threats are typically commercial or state-directed: ransomware, targeted espionage and sold-for-hire exploits. The cybersecurity sector grew in response, becoming a multibillion-dollar industry professionalized to meet that scale of threat.
Why smartphones changed defenders’ leverage
Hyppönen points to one clear technical win: modern platforms such as smartphones and hardened browsers have raised the price of effective exploits. When a zero-day costs hundreds of thousands or even millions of dollars to develop, only well-funded actors — usually state services — can afford them. For ordinary users, that has made a tangible difference in baseline security.
But some frontiers remain raw. Autonomous systems and remotely piloted vehicles combine physical danger with networked control, producing a category of risk that sits between classic cybersecurity and conventional defense.
Applying malware lessons to airborne threats
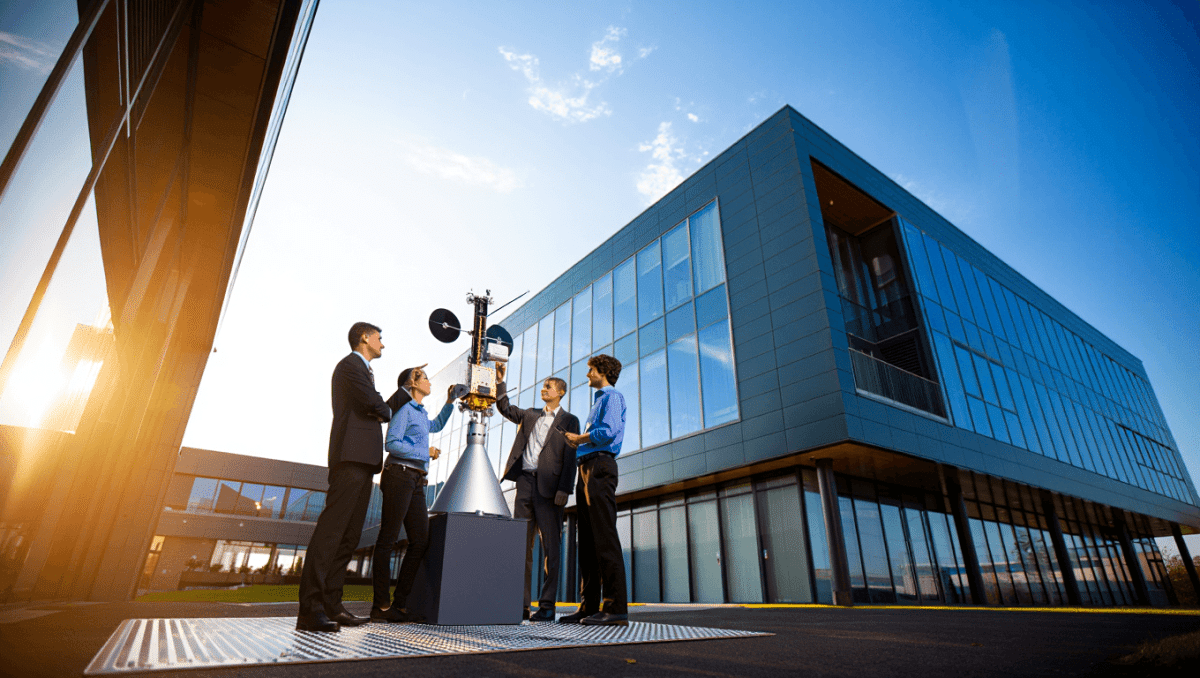
In mid-2025 Hyppönen accepted the role of chief research officer at a Helsinki firm building counter-drone systems for public authorities and military customers. The technical goal is familiar: identify signatures, detect anomalies and stop malicious activity before it causes harm. The vectors, however, are radio waves and flight controllers instead of file formats.
He explains the technical baseline simply: drones emit control signals. By capturing those transmissions — their radio fingerprints or IQ samples — defenders can reverse-engineer the command protocol and build detectors much like antivirus signatures. Once you understand the protocol, you can also craft targeted disruptions that interfere with a drone’s navigation.
“In the drone domain the first detection step often becomes the decisive one,” he said, describing how protocol weaknesses can allow swift intervention. “If you find the vulnerability, the threat can be neutralized quickly.”
The parallels with cyber defense extend beyond technique. Attackers adapt to countermeasures, defenders respond, and the cycle repeats. And for Hyppönen personally, the shift also maps onto a long engagement with threats originating near his country: the same geopolitical actors he tracked in cyberspace are now active in the air.
- Detection: Capture radio signals and build behavioral signatures to spot unauthorized aircraft.
- Interdiction: Jamming or protocol manipulation to sever an attacker’s control link.
- Attribution: Distinguish criminal misuse from state-directed operations — crucial for lawful response.
The stakes are concrete. In Ukraine, unmanned aerial systems have been a leading cause of battlefield casualties and infrastructure damage. For border nations and urban centers, unauthorized drones pose risks ranging from targeted strikes to large-scale surveillance and disruption.
What this means for policy and industry
Hyppönen’s move signals more than a career pivot: it illustrates how cybersecurity expertise is being redeployed to protect physical spaces. Governments and agencies will increasingly need capability in signal analysis, legal frameworks for interdiction, and rapid-response detection networks.
For the private sector, the expansion of anti-drone technologies creates demand for new toolsets and standards — but also questions about civil liberties and rules of engagement when devices are downed over populated areas.
Hyppönen frames his current work in human terms: defending people from machines that can inflict harm at distance. Whether the problem is a malicious email or an armed quadcopter, the essential task remains the same — detect the threat early and keep it from reaching those who would be harmed.
As conflict zones demonstrate how quickly unmanned systems can change the character of combat and crime, experts like Hyppönen are transplanting decades of malware-fighting experience into an emerging security domain. The next chapters in that story will be shaped by technical innovation, legal choices and how societies decide to balance safety, privacy and resilient airspaces.